Top 10 SEI Blog Posts of 2016
PUBLISHED IN
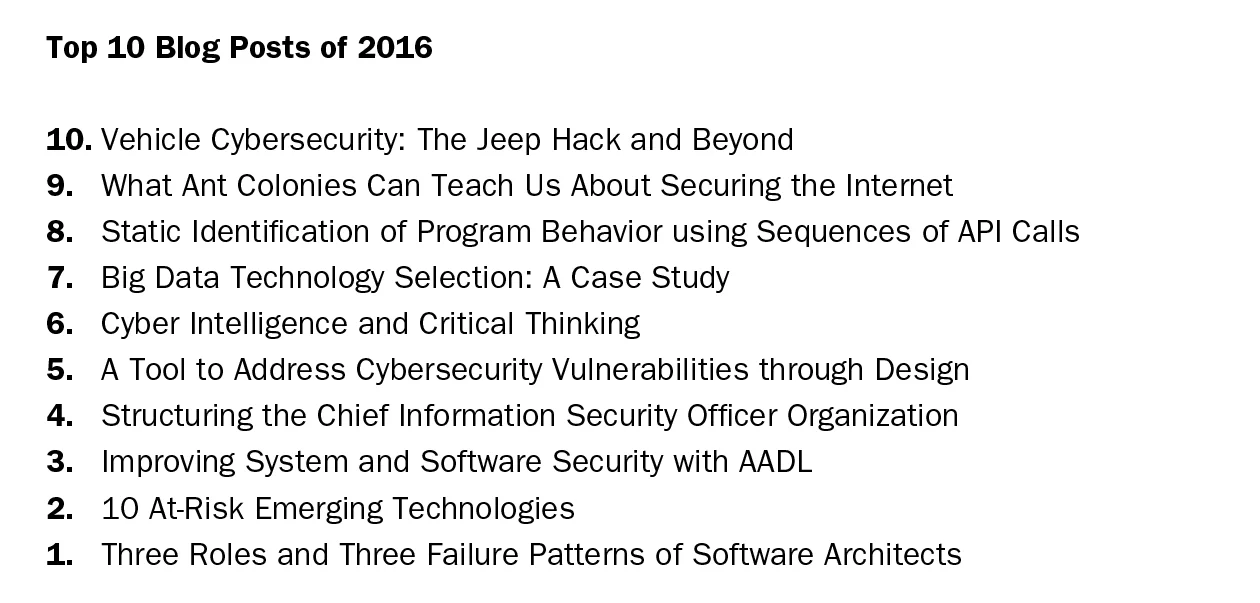
Software ArchitectureThe crop of Top 10 SEI blog posts published in the first half of 2016 (judged by the number of visits by our readers) represents a cross section of the type of cutting-edge work that we do at the SEI: at-risk emerging technologies, cyber intelligence, big data, vehicle cybersecurity, and what ant colonies can teach us about securing the internet. In all, readers visited the SEI blog more than 52,000 times for the first six months of 2016. We appreciate your readership and invite you to submit ideas for future posts in the comments section below. In this post, we will list the Top 10 posts in descending order (#10 to #1) and then provide an excerpt from each post, as well as links to where readers can go for more information about the topics covered in the SEI blog.
10. Vehicle Cybersecurity: The Jeep Hack and Beyond
by Christopher King and Dan Klinedinst
Automobiles are often referred to as "computers on wheels" with newer models containing more than 100 million lines of code. All this code provides features such as forward collision warning systems and automatic emergency braking to keep drivers safe. This code offers other benefits such as traffic detection, smartphone integration, and enhanced navigation. These features also introduce an increased risk of compromise, as demonstrated by researchers Chris Valasek and Charlie Miller (who work for Uber's Advanced Technology Center in Pittsburgh) in a July 2015 story for Wired, where they hacked into a Jeep Cherokee with a zero-day exploit. The Jeep Hack, as it has come to be known, highlighted an underlying issue for all vehicles: when automobiles are built, manufacturers focus on a threat model of potential risks that rely on physical defects, but do not include vulnerabilities that make a vehicle susceptible to intrusion and remote compromise. This blog post highlights the first phase of our research on making connected vehicles more secure by testing devices that connect into the vehicle itself.
Read the entire post.
View a webinar in which Dan Klinedinst and others from CERT discuss lessons learned from the Jeep Hack.
Read the white paper on this research, On Board Diagnostics: Risks and Vulnerabilities of the Connected Vehicle.
9. What Ant Colonies Can Teach Us About Securing the Internet
by Will Casey and collaborators Parisa Memarmoshrefi, Ansgar Kellner, Jose Andre Morales, Bud Mishra
In cyber systems, the identities of devices can easily be spoofed and are frequent targets of cyberattacks. Once an identity is fabricated, stolen, or spoofed it may be used as a nexus to systems, thus forming a Sybil Attack. To address these and other problems associated with identity deception researchers at the Carnegie Mellon University Software Engineering Institute, New York University's Tandon School of Engineering and Courant Institute of Mathematical Sciences, and the University of Göttingen (Germany), collaborated to develop a deception-resistant identity management system inspired by biological systems; namely, ant colonies. This blog post highlights our research contributions.
Read the entire post.
Read the paper Identity Deception and Game Deterrence via Signaling Games, which won best paper at the 9th EAI International Conference on Bio-inspired Information and Communications Technologies (formerly BIONETICS).
Watch a video describing our work.
8. Static Identification of Program Behavior using Sequences of API Calls
by Jeff Gennari
Much of the malware that we analyze includes some type of remote access capability. Malware analysts broadly refer to this type of malware as a remote access tool (RAT). RAT-like capabilities are possessed by many well-known malware families, such as DarkComet. As described in this series of posts, CERT researchers are exploring ways to automate common malware analysis activities. In a previous post, I discussed the Pharos Binary Analysis Framework and tools to support reverse engineering object-oriented code. In this post, I will explain how to statically characterize program behavior using application programming interface (API) calls and then discuss how we automated this reasoning with a malware analysis tool that we call ApiAnalyzer.
Read the entire post.
For more information on API call analysis and other tools check out the Pharos Static Analysis Tools site.
The SEI also has created a GitHub repository for Pharos, and plans to release selected components of our framework for inclusion back into the ROSE infrastructure.
7. Big Data Technology Selection: A Case Study
by John Klein
A recent IDC forecast predicts that the big data technology and services market will realize "a 26.4 percent compound annual growth rate to $41.5 billion through 2018, or about six times the growth rate of the overall information technology market." In previous posts highlighting the SEI's research in big data, we explored some of the challenges related to the rapidly growing field, which include the need to make technology selections early in the architecture design process. We introduced an approach to help the Department of Defense (DoD) and other enterprises develop and evolve systems to manage big data. The approach, known as Lightweight Evaluation and Architecture Prototyping for Big Data (LEAP4BD) helps organizations reduce risk and streamline selection and acquisition of big data technologies. In this blog post, we describe how we used LEAP4BD to help the Interagency Project Office achieve its mission to integrate the IT systems of the Military Health System and the Veterans Health Administration.
Read the entire post.
View the paper Application Specific Evaluation of NoSQL Databases that Klein co-authored with Ian Gorton, Neil Ernst, Kim Pham and Chrisjan Matser.
View the presentation A Systematic Presentation for Big Data Technology Selection, which Klein presented at the SEI's 2016 Software Solutions Conference.
6. Cyber Intelligence and Critical Thinking
by Jay McAllister
In June, representatives of organizations in the government, military, and industry sectors--including American Express and PNC--traveled to Pittsburgh to participate in a crisis simulation the SEI conducted. The crisis simulation--a collaborative effort involving experts from the SEI's Emerging Technology Center (ETC) and CERT Division--involved a scenario that asked members to sift through and identify Internet Protocol (IP) locations of different servers, as well as netflow data. Participants also sorted through social media accounts from simulated intelligence agencies, as well as fabricated phone logs and human intelligence. Our aim with this exercise was to help cyber intelligence analysts from various agencies learn to think critically about the information they were digesting and make decisions that will protect their organizations in the event of a cyberattack or incident and increase resilience against future incidents. This blog post, the second in a series highlighting cyber intelligence work from the ETC, highlights the importance of critical thinking in cyber intelligence, as well as a three-step approach to taking a more holistic view of cyber threats.
View the slides for the presentation, Be Like Water: Applying Analytical Adaptability to Cyber Intelligence, which McAllister presented at the 2015 RSA Conference.
5. A Tool to Address Cybersecurity Vulnerabilities through Design
by Rick Kazman and Carol Woody
Increasingly, software development organizations are finding that a large number of their vulnerabilities stem from design weaknesses and not coding vulnerabilities. Recent statistics indicate that research should focus on identifying design weaknesses to alleviate software bug volume. In 2011, for example when MITRE released its list of the 25 most dangerous software errors, approximately 75 percent of those errors represented design weaknesses. Viewed through another lens, more than one third of the current 940 known common weakness enumerations (CWEs) are design weaknesses. Static analysis tools cannot find these weaknesses, so they are currently not addressed prior to implementation and typically are detected after the software has been executed when vulnerabilities are much more costly and time-consuming to address. In this blog post, the first in a series, we present a tool that supports a new architecture model that can identify structures in the design and code base that have a high likelihood of containing bugs, hidden dependencies in code bases, and structural design flaws.
Read the entire post.
Read our paper A Case Study on Locating the Architectural Roots of Technical Debt, which I coauthored along with Yuanfang Cai, Ran Mo, Qiong Feng, Lu Xiao, Serge Haziyev, Volodymyr Fedak, and Andriy Shapochka.
The Titan software is being licensed by Drexel, and is available for academics. For more information, please visit https://drexel.edu/applied-innovation/about/contact/.
View the talk that Rick Kazman gave on this research called Locating the Architectural Roots of Technical Debt at the 2015 SATURN Conference.
View the presentation Hotspot Patterns: The Formal Definition and Automatic Detection of Architecture Smells by R. Mo, Y. Cai, R. Kazman, L. Xiao, from the Proceedings of the 12thWorking IEEE/IFIP Conference on Software Architecture (WICSA 2015).
4. Structuring the Chief Information Security Officer Organization
by Nader Mehravari and Julia Allen
Most organizations, no matter the size or operational environment (government or industry), employ a senior leader responsible for information security and cybersecurity. In many organizations, this role is known as chief information security officer (CISO) or director of information security. CISOs and others in this position increasingly find that traditional information security strategies and functions are no longer adequate when dealing with today's expanding and dynamic cyber-risk environment. Publications abound with opinions and research expressing a wide range of functions that a CISO organization should govern, manage, and perform. Making sense of all this and deciding on an approach that is appropriate for your specific organization's business, mission, and objectives can prove challenging. In this blog post, we present recent research on this topic, including a CISO framework for a large, diverse, U.S. national organization. This framework is the product of interviews with CISOs and an examination of policies, frameworks, maturity models, standards, codes of practice, and lessons learned from cybersecurity incidents.
Read the entire post.
Read the technical note Structuring the Chief Information Security Officer Organization.
Listen to the CERT podcast Structuring the Chief Information Security Officer Organization, featuring Julia Allen and Nader Mehravari.
View the SEI webinar Structuring the Chief Information Security Officer Organization, December 2015.
3. Improving System and Software Security with AADL
by Julien Delange
As our world becomes increasingly software-reliant, reports of security issues in the interconnected devices that we use throughout our day (i.e., the Internet of Things) are also increasing. This blog post discusses how to capture security requirements in architecture models, use them to build secure systems, and reduce potential security defects. This post also provides an overview of our ongoing research agenda on using architecture models for the design, analysis, and implementation of secure cyber-physical systems and to specify, validate, and implement secure systems.
Read the entire post.
Learn more about AADL.
View our SEI Webinar Architecture Analysis with AADL.
Read all of our SEI Blog posts on AADL.
2. 10 At-Risk Emerging Technologies
by Christopher King
In today's increasingly interconnected world, the information security community must be prepared to address vulnerabilities that may arise from new technologies. Understanding trends in emerging technologies can help information security professionals, leaders of organizations, and others interested in information security identify areas for further study. Researchers in the SEI's CERT Division recently examined the security of a large swath of technology domains being developed in industry and maturing over the next five years. Our team of analysts--Dan Klinedinst, Todd Lewellen, Garret Wassermann, and I--focused on identifying domains that not only impacted cybersecurity, but finance, personal health, and safety, as well. This blog post highlights the findings of our report prepared for the Department of Homeland Security United States Computer Emergency Readiness Team (US-CERT) and provides a snapshot of our current understanding of future technologies.
Read the entire post.
Read the technical report on which this blog post is based, 2016 Emerging Technology Domains Risk Survey.
1.Three Roles and Three Failure Patterns of Software Architects
by John Klein
When I was a chief architect working in industry, I was repeatedly asked the same questions: What makes an architect successful? What skills does a developer need to become a successful architect? There are no easy answers to these questions. For example, in my experience, architects are most successful when their skills and capabilities match a project's specific needs. Too often, in answering the question of what skills make a successful architect, the focus is on skills such as communication and leadership. While these are important, an architect must have strong technical skills to design, model, and analyze the architecture. As this post will explain, as a software system moves through its lifecycle, each phase calls for the architect to use a different mix of skills. This post also identifies three failure patterns that I have observed working with industry and government software projects.
Read the entire post.
View the SEI Webinar, What Makes a Good Software Architect?
Wrapping Up and Looking Ahead
In the coming months, look forward to posts highlighting our work in real-time extraction of biometric data, applying static analysis with classification models, and strategic prototyping for developing big data systems.
Additional Resources
Download the latest publications from SEI researchers at our digital library
https://resources.sei.cmu.edu/library/.
More By The Author
More In Software Architecture
PUBLISHED IN
Software ArchitectureGet updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In Software Architecture
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed
