Archive: 2021
Zero Trust Adoption: Managing Risk with Cybersecurity Engineering and Adaptive Risk Assessment
This SEI blog post provides an overview of zero trust and management of its risk with SEI's cybersecurity engineering assessment framework.
Read More•By Geoff Sanders
In Cybersecurity Engineering

Comparing DevSecOps and Systems Engineering Principles
This SEI Blog post compares and contrasts DevSecOps and Systems Engineering Body of Knowledge (SEBoK), discussing their shared goals and areas of divergence.
Read More•By Richard Turner
In DevSecOps

A Game to Assess Human Decision Making with AI Support
In decision-support systems based on AI, humans often make poor choices causing the systems to be abandoned. Rotem Guttman introduces a game that collects data on actual human decision making …
Read More•By Rotem D. Guttman
In Artificial Intelligence Engineering

The Current State of DevSecOps Metrics
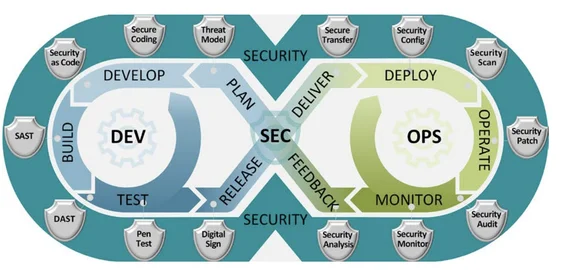
DevSecOps practices yield useful, valuable information about software performance that is likely to lead to innovations in software engineering metrics.
Read More•By Bill Nichols
In DevSecOps

The Latest Work from the SEI: Privacy, Ransomware, Digital Engineering, and the Solar Winds Hack
These publications highlight the latest work of SEI technologists in software architecture, digital engineering, and ransomware.
Read More•By Douglas Schmidt (Vanderbilt University)
In Software Engineering Research and Development

Generating Realistic Non-Player Characters for Training Cyberteams
This SEI Blog post describes efforts underway to improve the realism of non-player characters (NPCs) in training exercises with new software called ANIMATOR.
Read More•By Dustin D. Updyke, Tyler Brooks
In Cyber Workforce Development


When Your Software’s “Check Engine” Light Is On: Identifying Design Problems that Impact Software Failure
This blog post summarizes an effective roadmap for detecting design problems that can be used to improve software development and performance.
Read More•By Judy Hwang
In Software Architecture

Automating System Security with AADL: 11 Rules for Ensuring a Security Model
This SEI Blog post presents an approach for modeling and validating confidentiality using AADL, and 11 analysis rules for ensuring security model consistency.
Read More•By Aaron Greenhouse
In Software Architecture

Integrating Safety and Security Engineering for Mission-Critical Systems
Critical systems must be safe from harm and secure, but safety and security practices have evolved in isolation. The SEI is improving coordination between safety and security engineering.
Read More•By Sam Procter, Sholom G. Cohen
In Software Architecture


Aligning DevSecOps and Machine Learning
Luiz Antunes explores the machine learning (ML) and DevSecOps domains and proposes ways to use them in collaboration for increased performance.
Read More•By Luiz Antunes
In DevSecOps

SEI Blog Archive
Recent
Year