The Organizational Impact of a Modular Product Line Architecture in DoD Acquisition - Third in a Series
To maintain a strategic advantage over its adversaries, the Department of Defense (DoD) must field new technologies rapidly. "It is not about speed of discovery, it is about speed of delivery to the field," Michael D. Griffin, undersecretary of defense for research and engineering, told a Senate Armed Services subcommittee in April 2018.
The architecture of Department of Defenses (DoD) acquisition organizations is based on a big-bang/spiral development for systems of systems (SoS). This strategy has proved too slow and negates the opportunity to make small changes rapidly and deliver them on a continuum.
This post is the third installment in a series about modularity, open systems architectures, and product-line architectures for the DoD. This series has presented a proven set of best practices to help the DoD maintain its advantage: fully employ DevSecOps approaches, modularize designs, work more closely with system users, ship functionality in smaller increments more quickly, deliver near-term needed capability, and architect it all in a way that will pave the way to the future while improving the present. In this post, we explore how the implementation of these practices requires deep, fundamental changes in how the DoD is organized and how it executes its mission.
While it is easier to keep the current structure of the acquisition community intact, the cost of not changing has the unintended consequence of increasing risk to operational forces due to a lack of access to diverse sources of innovative alternatives. What's more, rejecting 21st century development methods increases program risk and extends development timelines, effectively reducing the value of the DoD's acquisition portfolio.
With commercial off-the-shelf (COTS) tools, platforms, and building blocks available to all nation states, near-peer competitors to the DoD are implementing new approaches and developing new technologies rapidly in key warfare areas faster than the DoD. "It is a dangerous and unpredictable time, and the United States must reverse any erosion in its military capabilities and capacities," General Joseph Dunford, Chairman of the Joint Chiefs of Staff stated during an interview at the Pentagon in October 2018. In this new era of near-peer competition, the DoD needs to evolve capabilities quickly and robustly to help warfighters as they face ever-changing challenges.
This series of blog posts, excerpted from a recently published paper, addresses these issues by proposing a DoD acquisition environment that is more efficient and capable of delivering much higher quality--with far greater innovation--in a fraction of the time. Our first post proposed a layered business and technical architecture model to help the DoD leverage modular component design practices that will establish more effective approaches for capability acquisition. In the second post, we explored this model in detail. In this third post, we examine key change drivers and technical and/or organizational structures associated with our proposed model of acquisition. We also examine the financial impact associated with the implementation and organizational structure of our proposed acquisition model.
Organizational Impact
When implementing a new acquisition model for the DoD, operations of the organization must evolve from the current program-of-record (PoR)-centric approach to one that values shared resources, direct and continuous user feedback, and focused investment on rapid military capability deployment. This type of change will be different and difficult to manage. A possible operating model for making this transition is outlined below. We suggest three major organizational entities that would eventually replace the traditional PoR environment, as shown in Figure 1.
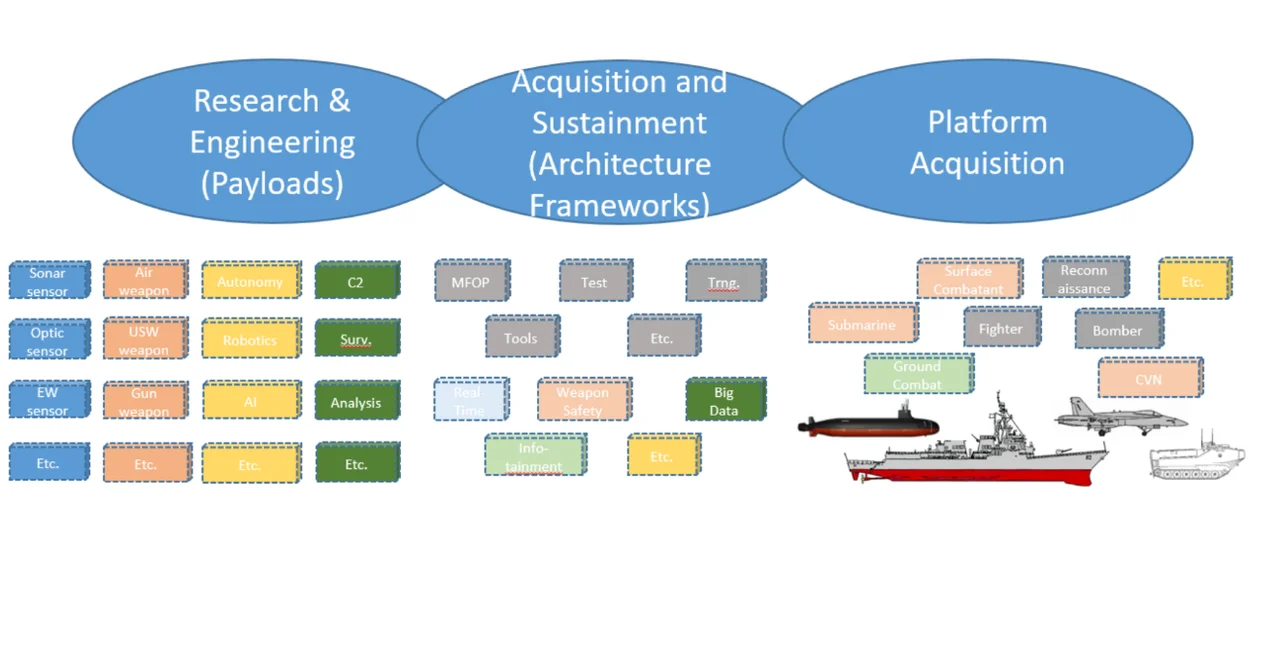
Figure 1: Future Acquisition Organizing Alignment. Source: Defense Innovation Board.
Vital to the success of this new operating model is a new type of partnership between the Joint Service leadership, the Service Acquisition Executives and the uniformed Service Chiefs. Instead of relying on a fixed requirements process, they will need to reinvent their how their organizations collaborate to deliver continuous improvement, informed by fast user feedback. This kind of speed-to-need is not possible with the existing "Program-of-Record" structure and will require new ways to manage enterprise assets and consistent deployment methods.
Each major entity shown in Figure 1 would shepherd a set of capability managers to ensure that interoperability and cooperation pervades the organization in the following ways:
- The research and engineering (R&E) arm within each service/agency would be populated with capability managers who manage a set of portable, cross-platform modular products. A balanced scorecard would be used to adjust modular capability allocation based on a distribution of the purposes that address the DoD's strategic needs, such as improving provider diversity or creating new venues for innovation. This scorecard would be shared with the four defense committees (the armed services and appropriations committees in both the House and Senate) so they can identify changes in spending policies and the allocation of associated appropriations.
- The acquisition and sustainment (A&S) arm would be staffed by architects and systems engineers who are focused on the strategic investment in the environment for fielding capability commodities. The development and deployment environments (e.g., Infrastructure-as-a-Service (IaaS) and Platform-as-a-Service (PaaS)) are strategic levers that are centric and primary to this plan, as they are to all modern companies (Amazon, Google, banks, etc.). These enterprise-wide strategic assets would manage the book-ends of this environment of (1) framework data architecture for information interoperability and (2) the technical environment to support modular capability commodities (product development support, module integration, hardware acquisition, etc.). A&S would work with the R&E community to provide artifacts, such as development kits, integration engines, test harnesses, compliance tools, virtual test bed and hardware definitions, and accreditation or certification platforms for delivery of capability modules. A&S would receive architecture-investment-related funds and all deployed hardware development and/or procurement funds. It would also be responsible for delivering certified capability directly to the platform.
- The platform acquisition arm would be responsible for acquisition and sustainment of the platforms that host the capability payloads (specific aircraft types, ships, tanks, submarines, satellites, etc.). They would also own the platform-unique capability requirements that flow down to both R&E for overall performance and to A&S for platform integration requirements.
Business and Contracting
The acquisition model described above is designed to support a robust and sustained landing pad for delivering a continuing stream of innovative modules of capability. The supporting business model is inherently risk prudent and affordable. It addresses the removal, replacement, addition, certification, and use of capabilities as discrete functional elements that can be independently acquired but that perform integrated functions. At least the following two distinct contracting models should be employed (both of which are already in place and supported by policy or statute):
- The overarching framework should be procured by the A&S arm described above. All innovators who want to deliver capability to the warfighter need to support the evolution of the environment (including architectural connectors and data models). These capabilities could be acquired and governed via a consortium model, for example, based on Other Transaction Authority and industry standards, such as the FACE Technical Reference Framework. The intellectual property strategy for this business environment should be based on collaboration, open standards, and consensus.
- Innovative warfighting functional capabilities should be acquired through the R&E arm described above. Its business relationships should be based on acquiring smaller units of capability in an agile manner and sustaining a diversity of candidate approaches to cutting-edge technologies. The strategy of the R&E arm would cultivate and retain organizations with deep expertise in technical or tactical areas. However, this engagement would last only as long as these providers can competitively deliver warfighting excellence against maturing and forecasted capability needs through a strategic research and development pipeline This model is superior to periodic competition, because any warfighting performance module can be removed and replaced when a new capability is ready for (re)use.
A model for establishing a cadre of performers that constantly innovate and compete to deliver these new capabilities will need a different contracting and payment model that rewards deployed capability and well-integrated functionality. In one variant of this model, the more software that is delivered, integrated, certified, and deployed, the more money the contractor would make. This model would also incentivize and generate new capability providers through direct industry investment.
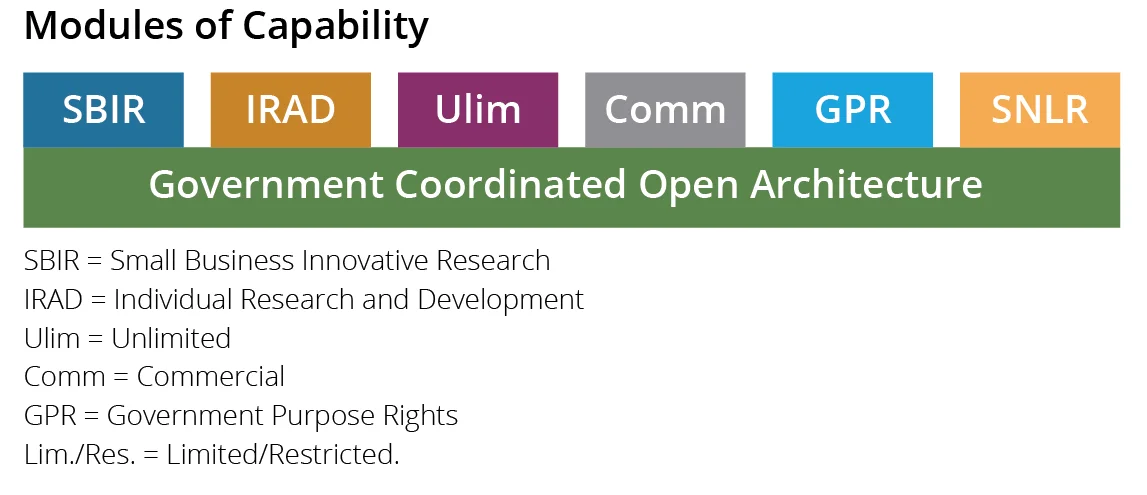
The intellectual property (IP) strategy for this business environment runs the full gamut of data rights, such as Small Business Innovative Research (SBIR), Industry Research and Development, (IRAD) Unlimited (Ulim), Commercial (Comm), Government Purpose (GPR), and Specially Negotiated License Rights (SNLR), as shown in Figure 2. The integration environment must be open to all practitioners and programs. Modules of capability can be removed, replaced, added, or modified with low technical risk. By lowering the costs, schedule, and technical burden of integration, test, and deployment, the government would not need to negotiate for more rights to share IP than the contractor should be bound to offer. The value of a certain capability is based on replicable functional performance, as well as prior investment.
The DoD must more artfully manage issues regarding delivery of detailed design data needed to perform test, evaluation, and accreditation activities that eliminate cyber vulnerabilities. This is divisive because, on the one hand, contractors doing business with the government want to protect their IP and/or data rights and, on the other, the government needs this information to complete necessary testing and evaluation. The government must become a trusted steward of industry's IP.
To attract a wide array of potential competitors, the government must also be more nuanced in exercising all of its data rights. In this way, legitimate use of rights to technical data can provide access to necessary information while shielding innovators and investors who have independently created designs (i.e., not based on government funding) from unfair practices, corrosive relationships, or counter-productive business threats.
Financial Architecture
The financial architecture needs to match the necessary investment in a technical architecture and the continuous evolution and deployment of capability. In particular, new incentives are needed to encourage cross-program coordination and product reuse. The current program element structure of the Planning, Programming, and Budgeting and Execution process will therefore need to be managed differently. Close coordination between the warfare sponsors in the Pentagon and the Program Executive Officers is needed to redesign the financial structure associated with development infrastructure as a cross-program resource.
At a minimum, cyber defense of all military software-intensive systems must be current and aggressively fielded. In addition, one of the most cost effective ways to improve military capability is to deploy new and innovative software solutions in concert with new hardware elements. Consequently, software-intensive systems must be updated continuously.
When it comes to the DoD Acquisition Framework, the definition of done must be revised for software-intensive products. As the Defense Science Board recently attested, software is never done. Consequently, management of a strategic resource, such as a set of technical reference frameworks, must be perpetually funded, and programs must be financially incentivized to use and contribute to this shared environment. In addition, after the basic capability of a product is completed, a continuous feed of funding must be made available until the program is completely removed from the field.
We assert that if there are sufficient funds to support the existing large number of independent programs and associated stove-piped systems, associated infrastructure, and development teams, then there are more than sufficient funds to support the proposed business model. The funding model will need to be changed over the course of several budget cycles to reflect the business model of continuous capability innovation and technology transition.
Acquisition programs must currently undertake extraordinary measures to justify resources for continuous improvement. They also eschew cross-program coordination and associated program risk. This type of coordination must become the normal mode of operation instead of the exception. Consequently, the financial architecture needs to value common approaches for continuous iteration and updates to accommodate a continuous engineering and product improvement lifecycle strategy. Financial incentives can include lower levels of oversight for programs leveraging shared resources and design infrastructure. New fiscal horizons can be established that go beyond the current Future Years Defense Program for products that have intrinsic value and show a frequent cadence for capability delivery.
Looking Ahead
In the next post in this series, we will examine how to build a technical architecture which will flow from the business architecture and begin with a set of technical reference frameworks that support the needs of military systems.
Additional Resources
This post was excerpted from a recently published paper, Capability Composition and Data Interoperability to Achieve More Effective Results than DoD System-of-Systems Strategies, which examines a new model of acquisition that applies a coherent set of methods to develop military mission capabilities as sets of composed modules.
Read an interview that Nick Guertin gave with Federal News Radio on how open systems are evolving to improve DoD buying power.
Read the SEI Blog Post by Don Firesmith Open Systems Architectures: When and Where to Be Closed.
More By The Authors
More In Software Architecture
PUBLISHED IN
Get updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In Software Architecture
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed


