It's Time to Retire Your Unsupported Things
"If it ain't broke, don't fix it." Why mess with something that already works? This is fair advice with many things in life. But when it comes to software security, it's important to realize that there can be severe consequences to using software or hardware after the vendor stops supporting it. In this blog post, I will discuss a number of examples of products, including Microsoft Windows and D-Link routers, whose continued use beyond their support periods may put you at unnecessary risk.
Support periods and information about consumer goods, including software, are regulated differently among jurisdictions, but this post focuses on encouraging you, as the user, to learn whether your devices are still supported and to make informed decisions in the event they're not.
Using any software beyond its end of life (EOL) is a dangerous choice. Why is this? Whenever a vulnerability is discovered in a product that has reached its EOL, the vendor will not fix it. These sort of vulnerabilities are referred to as forever days, which is a play on the term zero day that is used in the security field. That is, even though the vulnerability may be public and the vendor may be aware of it, the code will remain vulnerable indefinitely.
Microsoft Windows
When Windows XP was reaching its EOL in 2014, Microsoft warned its users:
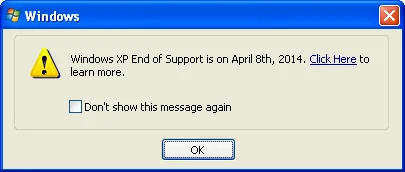
Microsoft has also made it abundantly clear that Windows 7 will no longer be supported after January 14, 2020. If you have been using your Windows 7 computer, you probably have seen some "nag" screens warning about the upcoming EOL status.
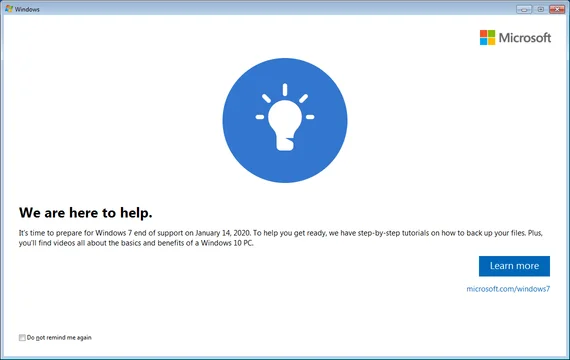
This Microsoft Windows example represents the best-case scenario: the vendor actively notifies users about EOL status with long lead times and the product is one with which the user has frequent interactions in which to receive these notifications.
Smartphones
Pushed Alerts
I have been using a smartphone since 2011, and I can say that I've never been pushed a warning when the device software has reached EOL from the vendor. That goes for both Android and iPhone devices.
OS Update Checks
If smartphones aren't receiving active alerts when they enter the EOL stage, what happens if a user manually checks for an OS update to stay secure?
Until recently, when you checked for an OS update, neither Android nor iPhone smartphones would notify you that support for a model had been discontinued. However, as of October 15, 2019, you might see a screen such as the following when checking for OS updates on some unsupported Google Nexus devices, such as the Nexus 5X:
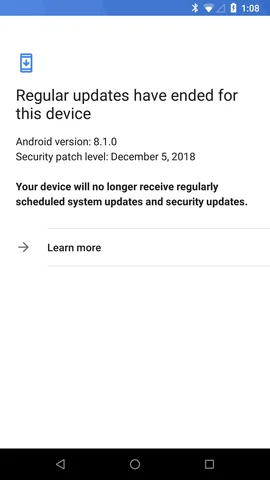
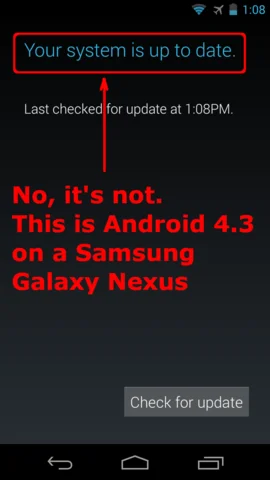
This is an improvement over Google's prior practice of simply stating "Your system is up to date," even though the device was running an older, unsupported version of Android. If you check for OS updates using a most Android phones or an Apple iPhone, you likely will not receive any indication that your phone is no longer supported.
On most other devices, you may see screens like these:

Support Timeframes
If you own a Google Pixel phone, you are guaranteed updates for at least 3 years from the date the device became available in the Google Store. If you have an Android phone that is not a Pixel, then it will likely receive security updates anywhere in the range of 0-3 years. That is, some discount Android devices may never receive security updates
Apple iPhone devices tend to receive security updates for a longer period of time. The iPhone 6S, for example, is still supported by the latest iOS 13 builds from Apple, despite being released over 4 years ago. It is not yet listed in the Apple Vintage and obsolete products page.
Home Wi-Fi Access Points
To summarize, Microsoft Windows tells you when its EOL is approaching. Smart phones have the ability to notify you about EOL, but they generally don't. What about things without screens, like home Wi-Fi routers? If you don't interact with a device, how will you know when its vendor has discontinued support?
Unless you've got one of those fancy smartphone-administered access points, the last time you probably interacted with your access point was during initial setup. How long ago was that?
Just like operating systems and smartphones, your home Wi-Fi access points and/or routers run software. And that software has bugs, which are occasionally discovered by security researchers. Do you know when you need to update your home access point's firmware? Are you running the latest firmware provided by the vendor? Is your device even supported by your vendor anymore?
D-Link Vulnerabilities
A vulnerability that affects multiple D-Link devices was discovered by Fortinet, which has assigned CVE-2019-16920 for tracking. This vulnerability has been reported to affect the following devices:
If you look at the support pages for these devices, you'll probably notice that the devices are all currently unsupported. Consequently, D-Link will not be providing fixes for CVE-2019-16920 for these devices. What does this mean for users of these devices?
As long as a vulnerable device remains in use, any website you visit will have the ability to silently reconfigure your router. Impacts include making your network accessible from the Internet, redirecting your banks' domain names to attacker-controlled sites, or other things you likely don't want to happen.
D-Link CVE-2019-16920 Proof of Concept
To demonstrate exploitation of CVE-2019-16920, I have created a proof of concept (PoC) exploit that will cause affected devices disconnect the network for a minute and then reboot. My PoC requires a button click to begin the test, but be aware that I manually inserted this requirement. Simply visiting a website with JavaScript enabled is enough for an attacker to compromise a vulnerable device.
Click here to view the PoC.
Please note that an HTTP connection is required for the PoC to function properly.
If your Internet connection temporarily dropped as the result of clicking the button in the above PoC, then it is imperative that you replace the device as soon as possible. You may wait a minute to regain internet connectivity, but be aware that continued use of the device may put your entire network at risk. Additionally, if you have confirmed that you have an affected device, but it is not in the list above, please send us a note with the details about what kind of device you have.
Final Thoughts
Many products have a limited support lifespan. You buy a product, that product, ideally, has a warranty period, but after the warranty expires you're on your own. If it breaks, you might fix it yourself, or find somebody else to fix it. And you continue to use the device as long as it is functional and it suits your needs.
Now, consider this situation with a modern Internet of Things (IoT) device, a refrigerator that has a computer screen on it, for instance. Or, how about a smart vacuum cleaner that uses your home Wi-Fi? What about a juicer that needs to phone home to ensure that you're authorized to juice the pack of fruit sitting in front of you? All of these things have software stacks. And those software stacks have a limited support lifespan.
When you purchased a device that has some sort of network connectivity, did you consider how long the vendor will support the software that runs it? Did the vendor even make that information available before you purchased the device? How will the device's behavior change once its support has reached EOL? What will happen to the device if the vendor decides to turn off a service the device relies on? Or what if the company goes out of business?
Recommendations
Any device that has a software stack associated with it may become unsafe when it has outlived its support life span. To help to protect yourself against attackers, consider the following actions:
- When making a purchasing decision, be sure to factor the vendor's support life span into your decision.
- Take an inventory of any devices you have that communicates with the Internet or your home network.
- For each device, determine whether the item is still supported by the vendor. This may require a bit of legwork with your favorite search engine, and it may even require contacting the vendor yourself.
- For any device that is still supported, ensure that it is running the latest software or firmware available from the vendor.
- For any device that has passed its EOL state, there are two viable options to help keep you safe:
- If Internet connectivity is not essential for the device functionality, take the device off of the network. In most cases, this may simply involve disassociating the device from your Wi-Fi network, or unplugging a network cable.
- If Internet connectivity is essential for the device to function properly (e.g. it's a smartphone or a router), then it's time to replace the device.
Now is the time to retire your unsupported things!
More By The Author
More In CERT/CC Vulnerabilities
PUBLISHED IN
Get updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In CERT/CC Vulnerabilities
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed
