COVID-19 and Supply-Chain Risk
Managing supply-chain risks from the new coronavirus outbreak is personally important to me. While my first concern--like everyone else's--is mitigating the direct public-health risk of the COVID-19 pandemic, I have a salient concern about the health-related risks that could be introduced if the global manufacturing supply chain for medical devices is disrupted: I'm a Type I diabetic who relies on a continuous glucose monitor (CGM) device to monitor my blood sugar and an insulin pump for insulin injections. In this blog post, I explore risk-management strategies that vendors can use to prepare and account for disruptions to hardware and software supply chains--disruptions that could affect devices that end users rely on.
Supply-Chain Risk Management
linked set of resources and processes between acquirers, integrators, and suppliers that begins with the design of ICT products and services and extends through development, sourcing, manufacturing, handling, and delivery of ICT products and services to the acquirer.
It is important to differentiate between software supply-chain risk and software supply-chain security risk. A 2014 SEI technical note defined risk as, "the probability of suffering harm or loss." It went on to define security risk as a measure of
(1) the likelihood that a threat will exploit a vulnerability to produce an adverse consequence, or loss, and (2) the magnitude of the loss.
The case of COVID-19 will directly impact software supply-chain risk, which may also create ancillary software supply-chain security risk. Risk management is needed to identify, analyze, and respond to the risks associated with the supply chain. The CERT Resilience Management Model (CERT-RMM) lists the following main goals for risk management: prepare, establish risk parameters and focus, identify risks, analyze risks, address risks, and use risk information to manage resilience. The CERT-RMM also includes a chapter on external dependencies management that specifically focuses on ensuring resilience when services or assets depend on actions of external entities, which is directly applicable to supply chains.
Supply-Chain Risk in Medical Devices
The two types of devices that I use to manage my diabetes operate independently. The output of a CGM (Figure 1), a blood-sugar reading, helps me calculate how much insulin to take so my blood sugar is controlled to prevent or reduce complications. A person with diabetes could use a CGM, an insulin pump (Figure 2), or both together.
If a key hardware component of these devices were to become unavailable or compromised because of realized risks to the supply chain, any users who depend on the device could have to switch to a new vendor or product or could be adversely affected by a newly emerging security vulnerability.

Figure 1: Continuous Glucose Monitor (CGM)
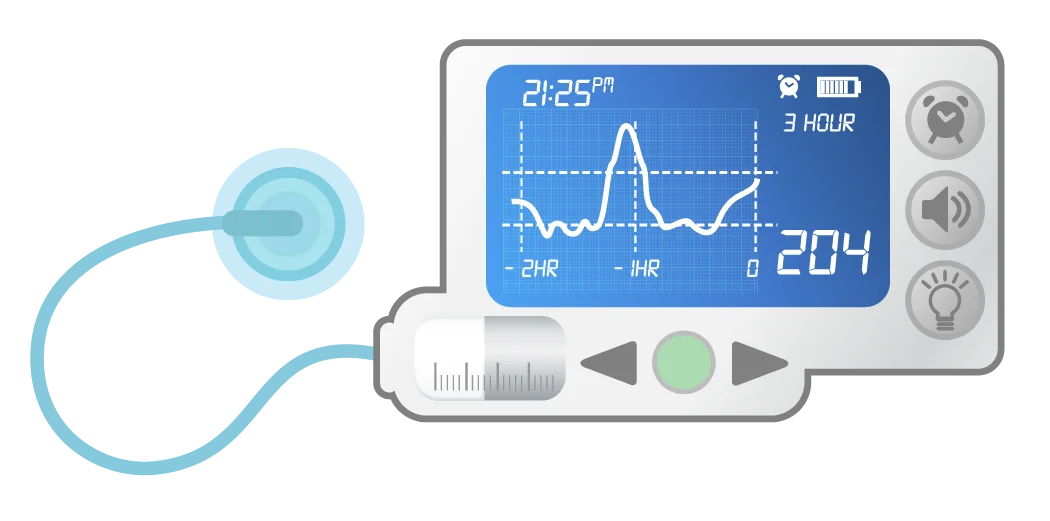
Figure 2: Insulin Pump
An insulin pump (Figure 2) commonly has a plastic shell, a circuit board with microcontroller, batteries, and a cannula or tube that delivers the insulin beneath the skin. Those and other parts must be sourced and assembled. The electronics mean that there is also a software supply chain. The software controls insulin delivery including scheduling, insulin ratios, correction ratios, alarms, and more. Modern pumps and CGM also communicate over radio frequencies, introducing software to manage communications in addition to the software managing the medication pump. Some devices also may send data back to the vendor's analytics platform to provide patients and doctors with deeper insights into trends and potential treatment improvements.
At the intersection of hardware and software, switching to an equivalent hardware component can cause software performance issues. For CGMs and pumps, new versions of devices often require new software, which might cover the device firmware, user interfaces on hardware, interfaces with mobile apps, software to transport data to the cloud, and interfaces for trusted third parties, such as family members or doctors. Software-compatibility requirements mean that any disruption in one link in the chain can lead to additional complications.
Sourcing and assembly are the parts of this supply chain that would most likely be disrupted as a result of the spread of the coronavirus. Software development, whether in-house or outsourced, may also experience varying degrees of impact from illness, social distancing, and quarantines. These disruptions could affect new software releases, upgrades, and security patches. Security could also be affected if disruptions result in the use of software with unknown vulnerabilities.
Risks that Pandemics and Other External Events Could Introduce
Even in the best of times, manufacturers are confronted with the risk of supply interruptions and delays, and the potential to receive corrupt components. The introduction of new products presents a special challenge. In the past, I have seen vendor of a novel device in the CGM market struggle to ship on time. To the vendor, a new product means retooling factories, finding new suppliers, training personnel in manufacturing and customer support, developing and distributing new software/firmware, clearing regulatory hurdles, and more. All these factors must be addressed while simultaneously trying to accurately forecast demand from current customers switching products or from new customers adopting the new product.
External events such as the current pandemic can hamper production, exacerbating existing supply-chain challenges and introducing new ones. Factors that could affect supply-chain performance include trade wars, raw-material shortages, recalls and safety scares, and climate change, among others. For example, some analysts believe that Apple's 5G iPhone will be delayed as a result of production disruptions in China. While a large company such as Apple could have the option of switching production to alternate factories in other countries, smaller companies have fewer options. On a more immediate level, we've seen common products such as disinfectant, wet wipes, toilet paper, and food staples out of stock in stores, showing that supply-chain risk leads to supply-chain failures when demand spikes or production is slowed.
The pandemic has introduced slowdowns, complexity, and heightened risk into global commerce. One technology example of risk emerging in the current pandemic environment is the widespread movement of software resources to the cloud. Increased use of cloud services is driven by the need for organizations to increase capacity quickly to accommodate changed work environments such as an increase in the number of employees who are working from home and who are conducting online meetings. Demand for cloud computing services has soared during the pandemic.
In previous SEI blog posts, we have identified best practices for cloud security and 12 risks, threats, and vulnerabilities in moving to the cloud. Cloud service providers and their services are part of the software supply chain, and organizations moving to the cloud must understand and account for the risks that such increased reliance represents, and how cloud adoption alters the organization's risk profile, reducing some risks while increasing others. Altering architecture and processes to leverage cloud computing advantages can also alter software security risks, for example by transferring some of the risk to the cloud service provider.
The Vendor's Point of View: Planning for and Responding to Supply-Chain Disruptions
How do vendors manage the risk of a supply-chain disruption? The Cybersecurity and Infrastructure Security Agency (CISA) issued the following recommendations for supplÂÂÂy chains as part of its publication related to COVID-19 risk management: Â
- Assess your organization's supply chain for potential impacts from disruption of transport logistics and international manufacturing slowdowns resulting from COVID-19.
- Discuss with those suppliers any challenges they may be facing or may expect to face due to the ongoing situation.
- Identify potential alternate sources of supply, substitute products, and/or conservation measures to mitigate disruptions.
- Communicate with key customers to keep them informed of any issues you have identified and the steps you are taking to mitigate them.
To understand risks in software, vendors must first understand all the software included in their devices. Software supply chains are increasingly complex, and an initial step in managing supply-chain risk is to identify the crucial pieces of software on which organizations rely. An effort by the National Telecommunications and Information Administration (NTIA), the Software Bill of Materials (SBOM), underscores the importance of transparency in addressing supply-chain risk. The NTIA's community-drafted SBOM is a nested inventory list of ingredients that make up software components. It provides detailed guidance on the "benefits of having an SBOM from the perspective of those who make software, those who choose or buy software, and those who operate it."
It is also important for vendors to understand all software dependencies. The ownership and responsibility for software may be scattered across several organizations, each of which may affect the security and integrity of the final product. A device vendor will have software dependencies related to their hardware and its operation, but also their whole infrastructure will depend on vendor software for operating systems, network devices, engineering programs, logistics, manufacturing plant management, and more.
Four Approaches to Secure the Supply Chain
Alternatives for vendors during supply-chain disruption will probably be constricted due to regulatory requirements, lower production, and/or shifts in demand. The best time for a vendor to start examining alternatives is when planning the supply chain, but the next best time is immediately. While it is always harder to fix things after they are implemented, it is never too late to conduct a full risk assessment, even if the immediate circumstances require a vendor to take shortcuts in the near term. The CERT-RMM provides guidance on managing operational risks to maintain resilience and can be used to initiate or mature risk-management programs.
The National Institute for Standards and Technology (NIST) Risk Management Framework for Information Systems and Organizations subdivides risk-management strategies for handling risks as accept, transfer, avoid, and mitigate. For suppliers, transferring or mitigating risks are the two achievable and reasonable strategies--to accept or avoid would put the entire business at risk. It seems unlikely that all supply-chain risk could be transferred, but some combination of insurance and agreements among vendors across the supply chain could transfer at least part of the organizational risk.
Approaches for mitigating risk include
- Source resources and assembly well ahead of time to provide a buffer against a short-term disruption.
- Monitor the situation and implement response/contingency actions when appropriate. A response/contingency action might be to start sourcing alternatives when inventory falls below a certain threshold. In this case, a long-enough pandemic could still cause disruption, but risk is reduced by providing a time cushion and developing contingencies.
- Offer incentives to supply-chain vendors if they maintain continuity of operations.
- Implement a recovery strategy to quickly restore the original supply chain and minimize the impact.
Whether or not a medical supplier has alternatives, being transparent with users about risks will help those users plan and more effectively manage their health. Customers generally react positively to transparency if supply-chain risk leads to disruptions that affect them. For example, in the case of customers with diabetes, helping them prepare by suggesting that they get a backup supply of test strips and finger lancets is a one way to minimize risk. Helping customers navigate obtaining an extra few months' supply of pumps or CGM supplies before supply-chain disruption is another option. Many vendors of diabetic supplies and other medical equipment have posted messages to their websites so that customers know whether their supply chains are experiencing disruption that could slow product deliveries.
These same principles of transparency and clear communication apply to all situations in which end users rely on vendors to supply products on which their health and well-being depend. Supply-chain risk is being amply demonstrated by the current pandemic, but proper planning and execution can help reduce organizational risks related to disruptions. In contrast, a lack of supply-chain visibility, poor planning, and panic can all contribute to confusion when dealing with supply-chain disruptions. A systematic approach can reduce this confusion and risk.
Although this post is by no means all-inclusive, I hope it provides some thoughtful information to help, and that organizations and individuals are able to endure the disruptions and then use their experience to become more resilient.
Additional Resources
Read the SEI blog post, 4 Elements in Securing the Telecommunications Supply Chain.
Read Assessing DoD System Acquisition Supply Chain Risk Management for general information about software supply-chain risk.
Read the SEI technical note, Evaluating and Mitigating Software Supply Chain Security Risks.
Read the SEI technical note, Introduction to the Security Engineering Risk Analysis (SERA) Framework.
Read the SEI white paper, An Approach for Integrating the Security Engineering Risk Analysis (SERA) Method with Threat Modeling.
Read the SEI white paper, CERT Resilience Management Model.
More By The Author
More In Situational Awareness
PUBLISHED IN
Get updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In Situational Awareness
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed
