Engaging the CSIRT Community: Cyber Capacity Building on a Global Scale
PUBLISHED IN
Cybersecurity Center DevelopmentAt the 2018 World Economic Forum, global leaders voiced concerns about the growing trend of cyberattacks targeting critical infrastructure and strategic industrial sectors, citing fears of a worst-case scenario that could lead to a breakdown of the systems that keep societies functioning. A painful example was the May 2017 WannaCry ransomware attack in which a worm rapidly spread through a number of computer networks, affecting more than 150 countries and more than 400,000 endpoints.
One of the largest victims of the WannaCry attack was the National Health Service in England and Scotland, where up to 70,000 computers, MRI scanners, and blood-storage refrigerators may have been affected. In this global threat environment, the need for Computer Security Incident Response Teams (CSIRTs) has become ever more critical. CSIRTs are expert teams that use their specialized knowledge and skills to detect and respond to computer security incidents. In the broader internet community, these teams form a "global network" from a diverse group of organizations and sectors, such as critical infrastructure, government, industry, and academia. In this blog post, the first in a series on CSIRTS, I talk about the work of CSIRTs and their importance in the global threat landscape.
Implementing a robust incident management capability enhances the ability of national governments and organizations to understand and respond to cyber threats. The Carnegie Mellon University Software Engineering Institute (SEI) defines a National CSIRT as "a computer security incident response team with National Responsibility (or National CSIRT) is a CSIRT that is designated by a country or economy to have specific responsibilities in cyber protection for the country or economy." National CSIRTs have taken a prominent role as points of contact in the coordination and response to national, regional, and international computer security incidents. Previous and current administrations have set forth cybersecurity policies that enable the United States to pursue international cooperation in maintaining a globally secure and resilient Internet with partner and ally nations. In 2014 the SEI's CERT Division and the U.S. Department of State's Office of the Coordinator for Cyber Issues (S/CCI), in coordination with the Department of Homeland Security's Office of International Affairs, began developing and implementing global cybersecurity capacity building activities that support capability and capacity building for national-level CSIRTs.
The CERT Division's International Cybersecurity Initiatives (ICI) Team and S/CCI collaborate with the global national CSIRT community, regional organizations, stakeholders from government, private sector, and the technical community, as well as relevant international organizations.
S/CCI-identified partner governments work with the CERT Division's ICI team to gather information about their national CSIRT to pinpoint where further development is needed and how to best utilize capacity building resources. The ICI team conducts workshops specific to CSIRT functions and provides guidance on developing internal workflows, policies, and standards.
We travel to different nations and train officials and staff on best practices and what to look for when training cybersecurity teams. Working side-by-side with partnering governments, the ICI team helps identify the best path forward for cyber capacity building in line with the four strategic goals that have been outlined for national CSIRTs. As outlined in the 2011 SEI Report Best Practices for National Cyber Security: Building a National Computer Security Incident Management Capability, Version 2.0, the four strategic goals for national CSIRTS include the following:
- Plan and establish a centralized computer security incident management capability (National CSIRT). For successful incident management, one of the first steps is to establish the incident management capability itself as a national CSIRT. It is beneficial to establish one source or point of contact for computer security incidents and cybersecurity issues. A single point of contact, such as a national CSIRT, provides a conduit for consistent, coherent messaging and provides stakeholders a single trusted source of information. In addition, the national CSIRT can encourage cybersecurity conversations and develop international cooperation on cybersecurity issues.
- Establish shared situational awareness. The primary function of the national CSIRT is managing computer security incidents and cybersecurity threats that are significant to national stakeholders. Initial steps in incident management focus on determining the scope and constituents of the national CSIRT, what types of information and communication technologies are used, and what types of incidents stakeholders are experiencing. Shared situational awareness is the general understanding of the environments within the scope of the national CSIRT.
- Manage incidents. As the trusted national cybersecurity resource, the national CSIRT must establish capabilities in areas such as incident response, containment, and service restoration to manage computer security incidents of national concern. The national CSIRT, however, might not assume all aspects of incident handling. Due to resource constraints or other factors, the national CSIRT may instead simply facilitate and coordinate analysis and response, engaging other national CSIRTs, technology vendors, or other expert organizations as needed.
- Support the national cybersecurity strategy. The national CSIRT works within the broader context of the national security strategy to monitor man-made, natural, physical, and cyber threats. The national CSIRT can:
- identify supplementary national strategic requirements for cybersecurity
- determine additional technical practices, improvements in education, and cybersecurity skills development for security personnel, including research and development staff
- recognize opportunities to further improve cyber security policy, laws, and regulations
- improve the measurement and metrics of costs associated with damages and cyber incidents
To help CSIRT teams achieve these goals, the CERT/CC contributed to the development of a list of services and functions a CSIRT can provide. In collaboration with the Forum of Incident Response and Security Teams (FIRST), a comprehensive list was created from the different perspectives of global FIRST members. The CSIRT Services Framework presents a hierarchical model that consists of the following levels:
- Service Area: This level includes related services, which are considered sets of recognizable actions.
- Service: The actions taken to achieve a specific result, for a desired outcome on behalf of the stakeholder or incident response team.
- Function. Functions include the means to fulfill the purpose of a specific service. When working in different countries, CSIRTs can have different functions based on the country they are trying to protect.
The CSIRT Services Framework is outlined as follows:
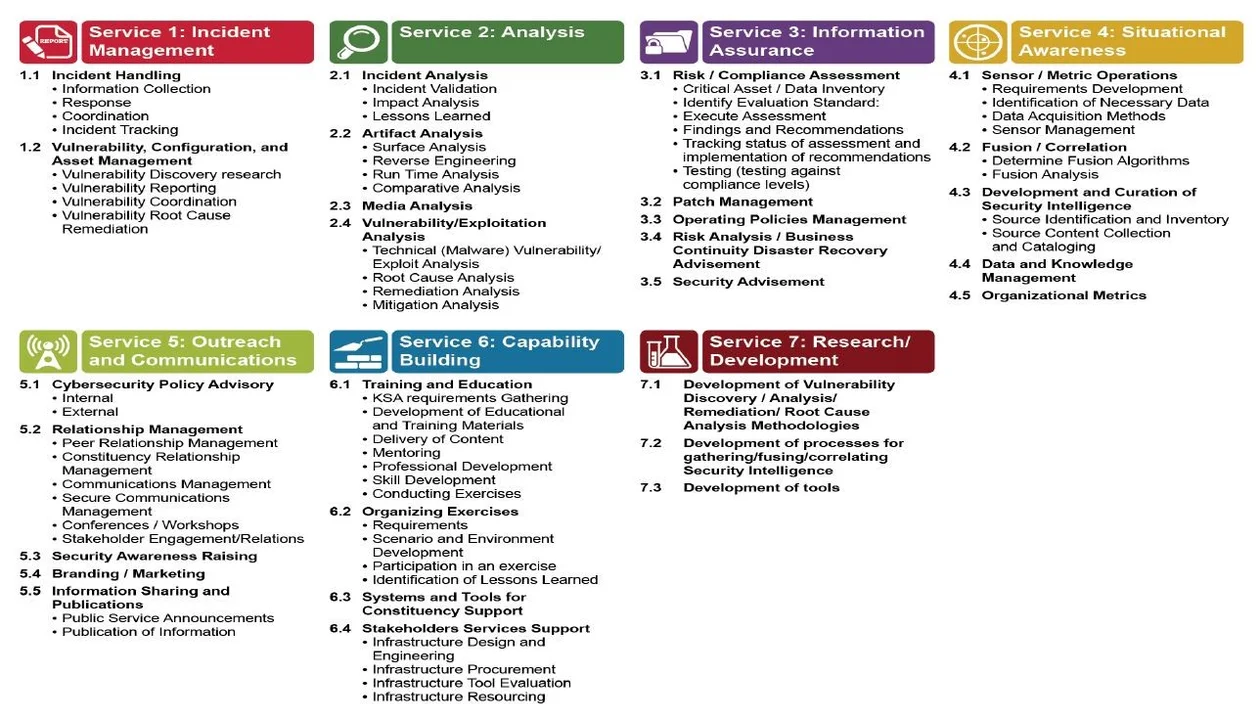
Service areas outlined in the CSIRT Services Framework include Incident Management, Analysis, Information Assurance, Situational Awareness, Outreach and Communications, Capability Building, and Research and Development. In working with international stakeholders, the ICI Team works with key personnel from the hosting nation to determine the current capacity of the CSIRT and identify areas for improvement. Working with the international stakeholder, an ICI team member will help select which service areas are best suited for the national CSIRT based on organizational mission.
Not every service area outlined in the CSIRT Services Framework might be needed by every CSIRT. Instead, the ICI team always emphasizes that CSIRTs, particularly resource constrained teams like National CSIRTs should select the most relevant services based on constituent needs and focus on providing high levels of service in those areas. Through proper planning and requirements identification, CSIRTs have the ability to start detecting and mitigating cyber threats effectively as they emerge.
Looking to the Future
The World Energy Council released a 2016 report predicting that the energy sector will be a prime target for cyber-attacks. Looking to the future, it seems a safe bet that CSIRTs will continue to play a critical role in maintaining the critical infrastructures that ensures power generation, food supply chains, and medical care. The next post in this series will provide details of a recent engagement in Cote d'Ivoire and delivery of a workshop on network analysis and Distributed Denial of Service mitigation.
Additional Resources
Read the SEI technical report Best Practices for National Cyber Security: Building a National Computer Security Incident Management Capability, Version 2.0.
Read the SEI whitepaper CSIRT Frequently Asked Questions (FAQ).
Read the FIRST CSIRT Framework.
Read the report Combatting Cyber Threats: CSIRTs and Fostering International Cooperation on Cybersecurity from the Global Commission on Internet Governance.
More By The Author
More In Cybersecurity Center Development
PUBLISHED IN
Cybersecurity Center DevelopmentGet updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In Cybersecurity Center Development
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed
