Reach Out and Mail Someone
Every day, we receive reports from various security professionals, researchers, hobbyists, and even software vendors regarding interesting vulnerabilities that they discovered in software. Vulnerability coordination--where we serve as intermediary between researcher and vendor to share information, get vulnerabilities fixed, and get those fixes out in the public eye--is a free service we provide to the world.
It's very important that we do all that we can to reach a vendor before disclosing vulnerability information, otherwise we've effectively dropped a 0-day on the vendor (please ignore the difficulty in defining that term, as Allen Householder points out in his previous blog post "Like Nailing Jelly To The Wall"). We're in the business of trying to prevent 0-days and not proliferate them; so we need a good strategy for getting in touch with vendors.
The Digital Era
Traditionally, we've relied on email as the best and fastest way to communicate with vendors and researchers. If we already have an email address for a vendor, then success! our report goes out immediately. But what if we don't have an email address? Our first thought is to check the vendor's website. Some vendors do a great job of advertising a contact email address for issues. (Some even have a specific email address only for security issues!) But for other vendors, it can be very difficult to locate any contact email address at all. Also, aggressive spam filters sometimes prevent contact.
Many vendors now list a general contact web form on their website instead of an email address. Unfortunately, we often do not receive a response from such web forms.
When email is unavailable, the next logical step is to attempt to call the vendor to establish contact. Typically, vendors only publicly list phone numbers for technical support, and it is often difficult to get the call escalated to someone that knows how to respond to security concerns. A common reason we cannot escalate is that the support team is unable to assist us without a customer ID number; usually we don't own the product in question, and our attempts to get by without an ID sometimes fail.
With the explosion of social media came a new way to contact vendors. Many vendors now make use of Twitter; however, these accounts are used more for marketing than support and we don't always obtain a response to inquiries. We've also looked at other social media such as LinkedIn to find contacts, but often such networks require previous connections ("friending" or "following") before contact information can be seen, creating a chicken-and-egg scenario.
Thus, despite so many potential contact channels, we often find that plaintext email is still the best way to reach someone about security issues.
Unfortunately, the problem of finding suitable security contacts is only becoming more difficult with the explosion of internet of things (IoT) devices; more and more vendors exist today that did not exist yesterday. Some of these vendors are also new to managing a security response to vulnerabilities in their products and do not have an established process for reporting a vulnerability or even a good contact email. (These difficulties are described in Allen's blog post, What's Different about Vulnerability Analysis and Discovery in Emerging Networked Systems?)
The Old-Fashioned Way
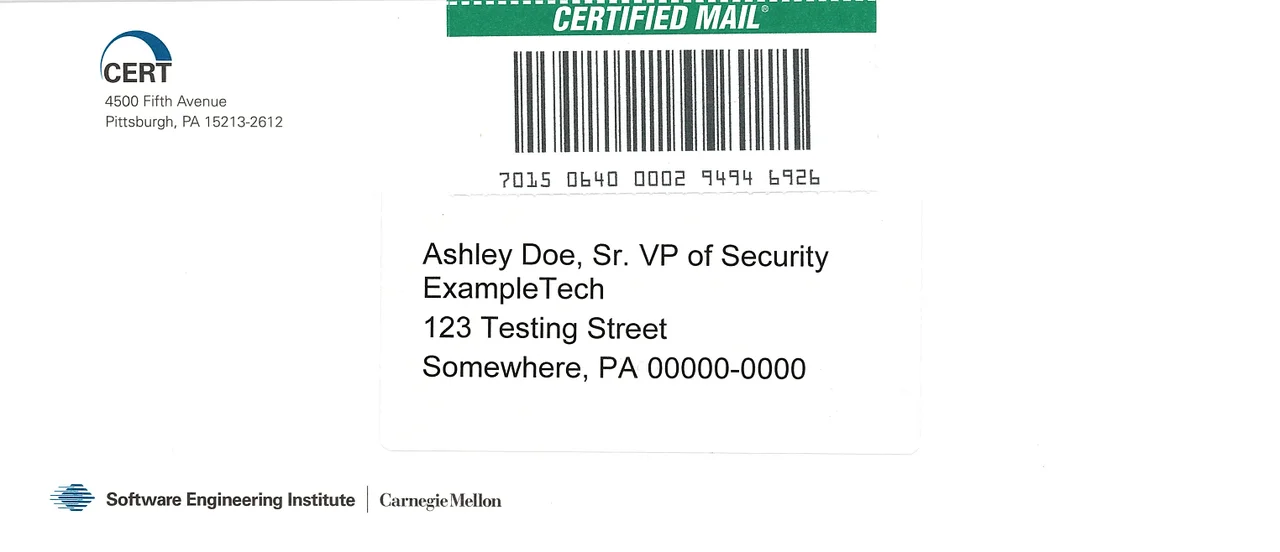
Recently we started piloting a new idea using old technology: reaching out to vendors via the post office. If email and other methods fail, we'll move on to sending a physical letter.
From various sources, we attempt to find the names of people in engineering or security departments, and send letters to these people at their business/corporate office address. The letter alerts them to the presence of vulnerabilities in their product, our previous attempts at contact, our intention of publishing, and our contact information to start the dialog. The letter is on CERT Division letterhead and stuffed in a CERT-labeled envelope. We'll send it USPS certified mail inside the U.S. and via private courier with delivery confirmation to international addresses.
It is our hope that these letters will open up conversations with vendors (especially ones totally new to the process; we're glad to work with you) and establish a good point of contact for any future vulnerability coordination efforts.
So far, we've seen success; for example, one vendor responded positively to our letter, stating that email spam filters were actually hiding some security reports in their mail system, and our letter alerted them to the problem so that they could fix it.
Staying In Touch
Feel free to get in touch with us at cert@cert.org if you would like to establish contact or update your contact information with us. What we need from you is easy: let us know the best way to reach you (primary email address), and if that email is shareable or private. For example, is it ok if a security researcher communicates with you directly? Include any other contact information you'd like to share such as phone numbers is good too!
If your company or organization does not already have one, consider establishing a security email alias (such as security@vendor.com) to allow easier communication with the CERT/CC and others that wish to help you find and fix software vulnerabilities.
For secure communication, we recommend establishing a PGP key for your security email alias or other email address. Once the key is established, please send the public PGP key to us at cert@cert.org.
Our team members often attend various conferences and events; if you happen to see someone from CERT at an event, feel free to say hi and establish contact with us!
More By The Author
More In CERT/CC Vulnerabilities
PUBLISHED IN
Get updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In CERT/CC Vulnerabilities
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed
