Risk
Blog Posts
2 Approaches to Risk and Resilience: Asset-Based and Service-Based
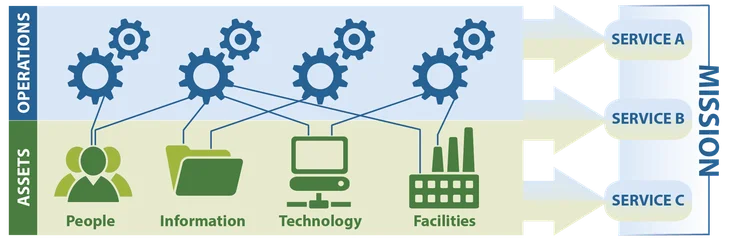
There are benefits and challenges of the two approaches to risk and resilience management: one based on an organization’s assets and the other on its services.
• By Emily Shawgo
In Enterprise Risk and Resilience Management

IT, OT, and ZT: Implementing Zero Trust in Industrial Control Systems

This blog post introduces fundamental ZT and ICS concepts, barriers to implementing ZT principles in ICS environments, and potential methods to leverage ZT concepts in this domain.
• By Brian Benestelli, Daniel J. Kambic
In Enterprise Risk and Resilience Management


Translating the Risk Management Framework for Nonfederal Organizations

This blog post translates federal-government-specific aspects of the Risk Management Framework into processes for nonfederal organizations.
• By Emily Shawgo, Brian Benestelli
In Enterprise Risk and Resilience Management


Potential Implications of the California Consumer Privacy Act (CCPA) for Insider Risk Programs
This blog post reviews the general framework of the California Consumer Privacy Act (CCPA), describes specific implications for insider risk management, and provides recommendations to prepare insider risk programs to …
• By Emily Kessel, Sarah Miller, Carrie Gardner
In Insider Threat


Zero Trust Adoption: Managing Risk with Cybersecurity Engineering and Adaptive Risk Assessment
This SEI blog post provides an overview of zero trust and management of its risk with SEI's cybersecurity engineering assessment framework.
• By Geoff Sanders
In Cybersecurity Engineering

10 Steps for Managing Risk: OCTAVE FORTE
This post, adapted from a recently published technical note, outlines OCTAVE FORTE's 10-step framework to guide nascent organizations as they build an ERM program and mature organizations as they fortify …
• By Brett Tucker
In Enterprise Risk and Resilience Management

Evaluating Threat-Modeling Methods for Cyber-Physical Systems
Addressing cybersecurity for a complex system, especially for a cyber-physical system of systems (CPSoS), requires a strategic approach during the entire lifecycle of the system....
• By Nataliya Shevchenko
In Enterprise Risk and Resilience Management

Threat Modeling: 12 Available Methods
Almost all software systems today face a variety of threats, and the number of threats grows as technology changes....
• By Nataliya Shevchenko
In Enterprise Risk and Resilience Management

Malware Analysis, Acquisition Strategies, Network Situational Awareness, & Cyber Risk - The Latest Research from the SEI
This SEI Blog post presents the SEI's latest research on malware analysis, acquisition strategies, network situational awareness, and cyber risk management.
• By Douglas Schmidt (Vanderbilt University)
In Enterprise Risk and Resilience Management

A Taxonomy for Managing Operational Cybersecurity Risk
This SEI Blog post discusses large-scale cyberattacks on payment card systems and a recent effort to create a taxonomy for operational cybersecurity risks.
• By James J. Cebula
In Enterprise Risk and Resilience Management
