Insider Threat Incident Analysis: Court Outcome Observations
In the United States, legal cases may be tried in criminal court or civil court. According to data in the CERT National Insider Threat Center (NITC) incident corpus, the type of court makes a big difference in the legal outcomes of insider attack cases. This blog post analyzes these differences, specifically sentencing and restitution in criminal cases and findings of liability in civil cases. This blog post does not, and is not intended to, constitute legal advice. Please consult legal counsel on any specific matter.

Criminal court punishes parties found guilty of committing a crime and may allow victims to recover for damages they suffered. Punishment includes incarceration, supervised release, and restitution, which is a monetary value of calculable impact to the victim. Civil court is intended to allow victims to recover for more than the calculable damages, by factoring in harm the victim may have suffered and potential future loss.
While there are many differences between criminal and civil courts, including burden of proof requirements, our analysis of insider incidents in the NITC incident corpus focused on sentencing and damage recovery. The analysis below examines differences in the outcomes of civil or criminal insider incidents, based on available data. For criminal cases, that data is primarily about sentencing and restitution; for civil cases, liability.
Criminal Court Outcomes versus Civil Courts Outcomes
Across the incident corpus, the three most frequently occurring incident types are fraud (743 incidents), sabotage (152 incidents), and theft of intellectual property (IP) (127 incidents). In fraud incidents, an insider uses information technology (IT) to exceed their access to protected information for personal gain or to steal information that could be used to commit inherently financial fraudulent acts. In theft of IP incidents, an insider steals IP from an organization. In sabotage incidents, an insider uses IT to direct specific harm at an organization or individuals within an organization. Our incident coding process maps legal facts to a certain incident type, allowing for an analysis of differences in court outcomes across the different incident types and court systems.
Criminal Court Trends
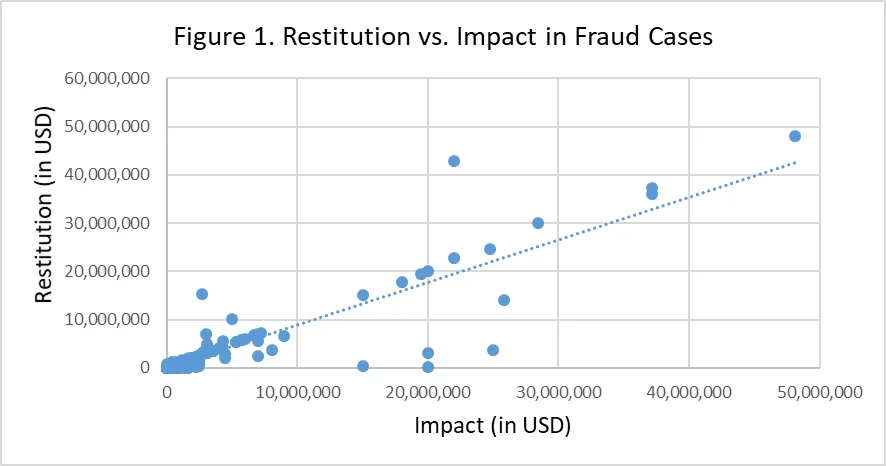
Fraud incidents were the highest frequency to be brought before a criminal court, representing 73% of criminal cases in the incident corpus. Due to the inherently financial nature of fraudulent activity, most organizations are able to trace and calculate specific damages. In the fraud incidents in our corpus, the average financial impact was $2.8 million and the average restitution was $2.75 million.
Because financial damage is often traceable, awards in fraud cases are often equal to actual losses, as shown by the trend line in Figure 1. The outliers in this graph represent cases in which the impact to the organization was difficult to measure because of factors such as loss of reputation or untraceable funds, which prevented the court from deriving exact impact calculations.
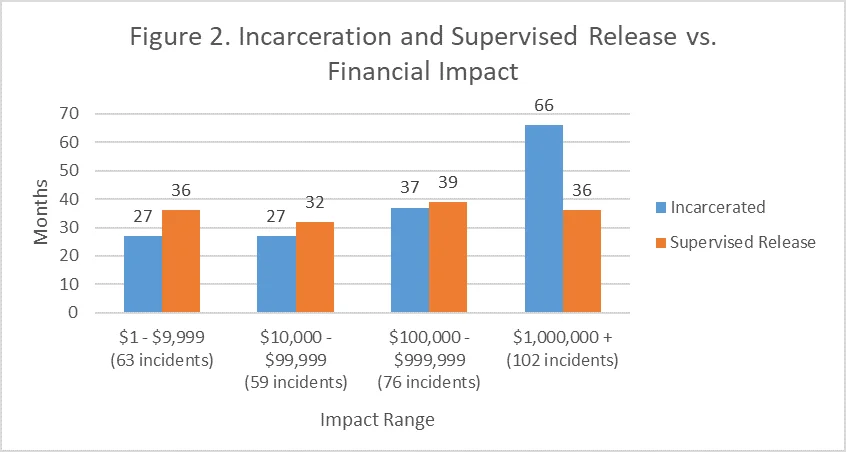
Insiders found guilty of fraud spent, on average, 39 months in prison. However, Figure 2 demonstrates that incarceration terms vary with the calculable financial impact to an organization. In contrast, supervised release terms are consistent across financial impact levels. This consistency in supervised release terms is common among all three incident types.
One reason for the lower number of theft of IP and sabotage incidents brought to criminal court, compared to fraud, may be the difficulty in measuring the damage these events cause victim organizations. Financial damage is often difficult to calculate, leaving victim organizations to estimate it.
According to our incident corpus data, in theft of IP incidents brought to criminal court, the average (estimated) impact is $15 million, while the average (actual) restitution is $900,000. The average (estimated) impact in sabotage incidents brought to criminal court is $1.3 million, while the average (actual) restitution is $300,000. The spread between reported financial impact and awarded restitution indicates the difficulty in assessing the actual damage, and criminal courts often settle on a lower number than the victim organizations attempt to prove.
Incarceration and supervised release outcomes in theft of IP and sabotage incidents tend to vary. In incidents with more speculative damages, courts may sentence the insider to longer incarceration times because of the difficulty in calculating restitution. This strategy may reflect the justice system's intent to deter re-offenders, but it can inhibit victim organizations from fully recouping financial damages, triggering separate civil suits to recover the difference.
Civil Court Trends
While fraud incidents are often brought to criminal court, theft of IP and sabotage incidents are often brought to civil court because of victims' difficulty in recovering speculative damages in criminal court. Some civil cases settle outside of court and are dismissed mid-trial, lessening the need for the victim organization to reveal sensitive information in discovery. Figure 3 indicates that more than half of the theft of IP incidents and about a fifth of sabotage incidents were dismissed.
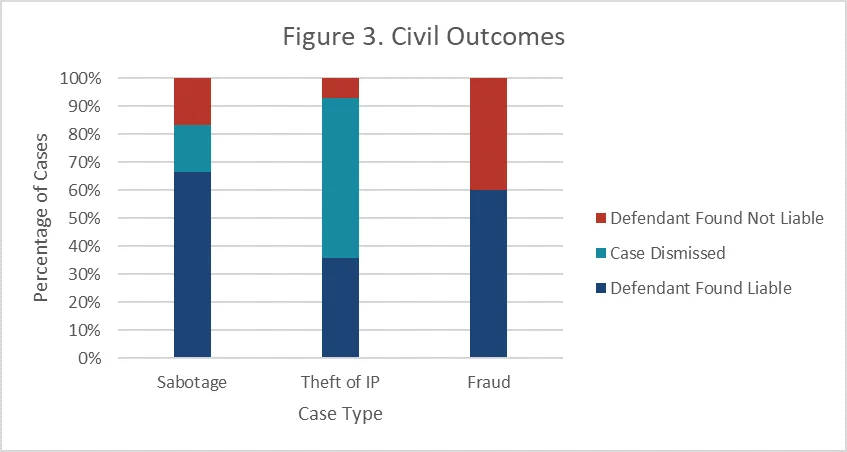
Occasionally, criminal cases will precede civil cases involving theft of IP and sabotage. In general, after a criminal court case has concluded, the victim organizations may choose to bring civil suits against an insider. Though they still have to prove that speculative damages exist, victims have an easier time proving misconduct by the insider because of the previous criminal proceedings.
Courts award punitive and general damages in civil cases to provide relief based on the insider's character and the victim's potential future loss. Civil courts provide an additional avenue of potentially full financial recovery from insider incidents, especially for speculative damages if they can be proven reasonable. In sabotage incidents, damages are typically for loss or tarnishing of reputation. In theft of IP cases, damages are usually for loss or release of proprietary information. Civil courts also help protect against future loss or damage, as in theft of IP cases where insiders often must sign a non-disclosure contract or an enjoinment agreement.
The Type of Court Matters
Criminal and civil courts provide victims of insider attacks different legal pathways for recovering damages and different potential outcomes. The trends analyzed show fraud victims are typically able to recover their calculable damages in criminal court, while theft of IP and sabotage victims are able to recover damages in civil court. Send us your thoughts on the intersection of insider incidents and the justice system to insider-threat-feedback@cert.org.
More In Insider Threat
PUBLISHED IN
Get updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In Insider Threat
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed
