InTP Series: Conclusion and Resources (Part 18 of 18)
The intent of this blog series was to describe a framework that you could use as you build an insider threat program (InTP) in your organization. We hope you found it a useful resource and recommend that you refer back to it as you progress through the Initiation, Planning, Operations, Reporting, and Maintenance phases of building your InTP.
Hi, this is Randy Trzeciak, Technical Manager of the CERT Insider Threat Center in the CERT Division of the Software Engineering Institute. It is my privilege to write this final installment of the InTP blog series.
Keep in mind that building an effective InTP does not happen overnight. It is a long-term effort that needs to be incorporated into your enterprise-wide risk management program. It cannot be achieved simply by purchasing a tool or technology, although tools are an important component of an InTP. Start small by focusing on protecting what's most critical to your organization and gradually increase the scope of the InTP over time.
We recommend that you review the components of an InTP as you build one in your organization.
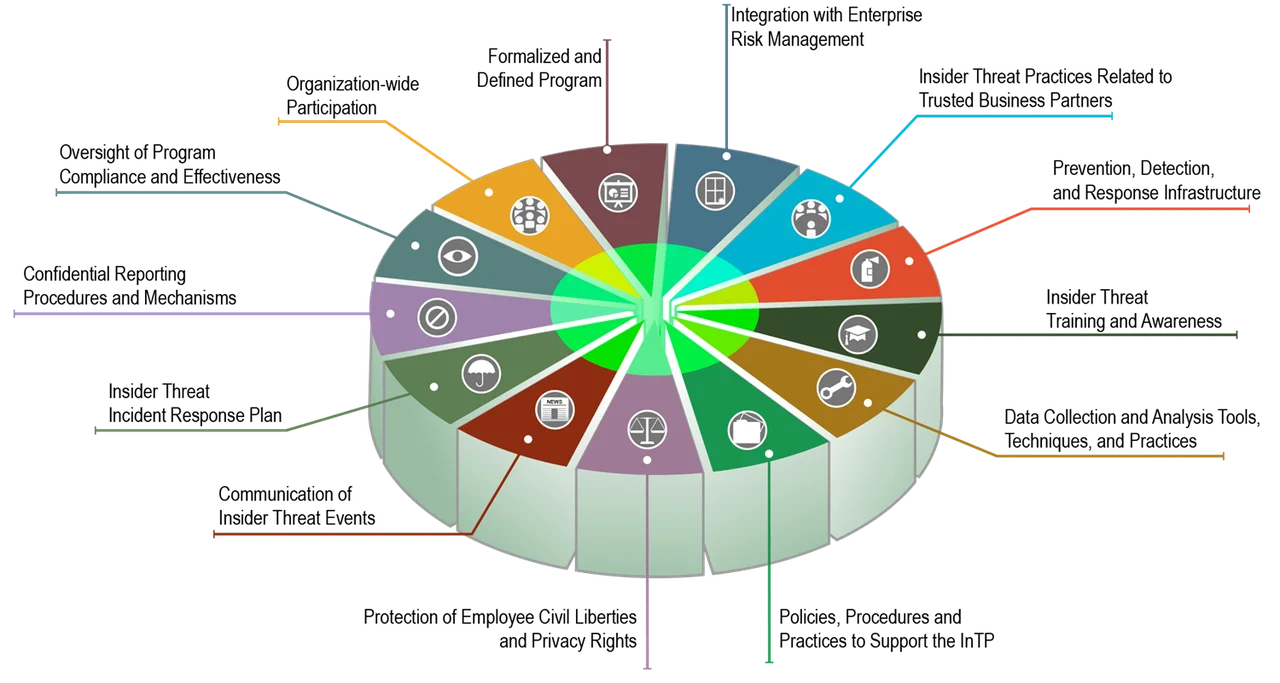
Establishing an Insider Threat Program (view full-size image)
InTP Guiding Principles
- Key Elements of an Insider Threat Program
- The Formalized Program
- Participation of Business Areas
- Oversight of Program Compliance and Effectiveness
- Integration with Enterprise Risk Management
- Prevention, Detection, and Response
- Training and Awareness
- Confidential Reporting
- Trusted Business Partners
- Data Collection and Analysis
- Incident Response Planning
- Communicating Insider Threat Events
- Policies, Procedures, and Practices
- Protection of Employee Civil Liberties and Privacy Rights
- The Insider Threat Framework
- Developing an Implementation Plan
- Conclusion and Resources (this post)
Throughout this blog series we acknowledge that we're not able to provide sufficient detail to provide everything you need to build your program, but we can point you to the resources you need.
If you are looking for in-depth training on how to build your program, would like to obtain an Insider Threat Program Manager Certificate, or would like our team to help you build or evaluate your program, please visit https://www.sei.cmu.edu/research-capabilities/all-work/display.cfm?customel_datapageid_4050=21232, or contact the SEI at 412-268-5800.
PUBLISHED IN
Get updates on our latest work.
Sign up to have the latest post sent to your inbox weekly.
Subscribe Get our RSS feedMore In Insider Threat
Get updates on our latest work.
Each week, our researchers write about the latest in software engineering, cybersecurity and artificial intelligence. Sign up to get the latest post sent to your inbox the day it's published.
Subscribe Get our RSS feed